Blog / Security Vulnerability in Hub Vault Unlock: Update Required
We have released an important security fix for all Cryptomator client apps, which fixes a vulnerability affecting all users who unlock Hub-managed vaults.
Required Action
Please update all your Cryptomator client applications that access Hub-managed vaults immediately to the fixed versions:
You can also find all downloads on our downloads page.
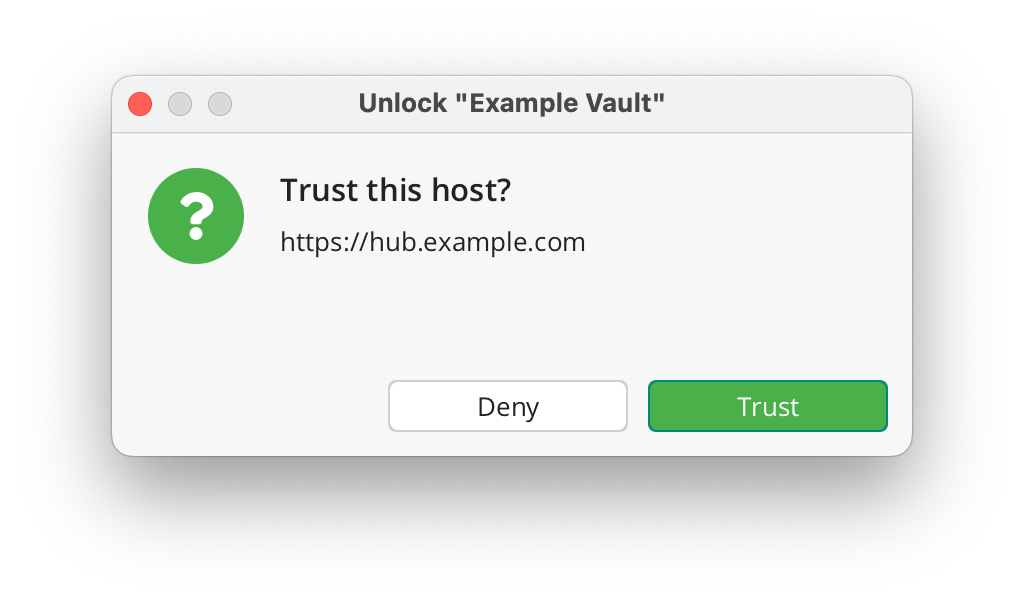
After the update, Cryptomator clients connecting to self-hosted Hub instances will show a one-time “Trust this host?” dialog that must be confirmed individually. Before accepting, please verify that the displayed Hub URL is correct and matches your Cryptomator Hub instance. Clients connecting to Cryptomator Hub Managed are not affected by this dialog, as managed domains are trusted automatically.
Are my vaults safe?
Yes. Since Cryptomator Hub uses end-to-end encryption, vault data was never in danger.
Which vaults are affected?
The vulnerability lies within the unlock workflow of Hub-managed vaults. Local vaults are unaffected.
What data is at risk?
An attacker with write access to your encrypted data could tamper the vault in a way that makes Cryptomator send a session token to a malicious server. The exfiltrated token can then be used to impersonate a user to access unencrypted information like usernames, vault names, etc. in Hub.
Has this been exploited?
At this time, we have no evidence of active exploitation of this vulnerability.
Security Advisories
As part of responsible disclosure, the full security advisories will be published on March 20. Until then, the following links will not work yet — this is expected and intentional:
- Desktop: CVE-2026-32303
- Android: CVE-2026-32317
- iOS: CVE-2026-32318
How can I get help?
If you have any further questions or need assistance during updates, don’t hesitate to contact us at [email protected].